Turingery
Turingery[1] or Turing's Method[2] (playfully dubbed Turingismus by Peter Ericsson, Peter Hilton and Donald Michie[3]) was a hand codebreaking method devised in July 1942[4] by the mathematician and cryptanalyst Alan Turing at the British Government Code and Cypher School at Bletchley Park during World War II.[5][6] It was for use in cryptanalysis of the Lorenz cipher produced by the SZ40 and SZ42 teleprinter rotor stream cipher machines, one of the Germans' Geheimschreiber (secret writer) machines. The British codenamed non-Morse traffic "Fish", and that from this machine "Tunny".
Reading a Tunny message required firstly that the logical structure of the system was known, secondly that the periodically changed pattern of active cams on the wheels was derived, and thirdly that the starting positions of the scrambler wheels for this message—the message key—was established.[7] The logical structure of Tunny had been worked out by William Tutte and colleagues[8] over several months ending in January 1942.[9] Deriving the message key was called "setting" at Bletchley Park, but it was the derivation of the cam patterns—which was known as "wheel breaking"—that was the target of Turingery.
German operator errors in transmitting more than one message with the same key, producing a "depth", allowed the derivation of that key. Turingery was applied to such a key stream to derive the cam settings.[10]
The SZ40 and SZ42
The logical functioning of the Tunny system was worked out well before the Bletchley Park cryptanalysts saw one of the machines—which only happened in 1945, shortly before the allied victory in Europe.[11]
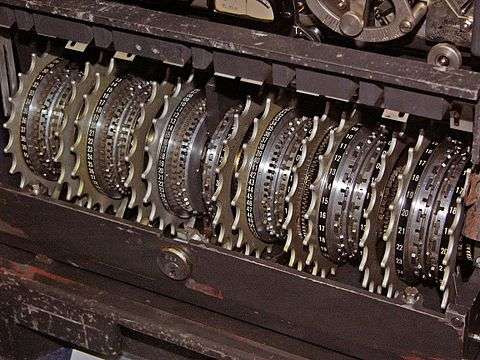
The SZ machines were 12-wheel rotor cipher machines which implemented a Vernam stream cipher. They were attached in-line to standard Lorenz teleprinters. The message characters were encoded in the 5-bit International Telegraphy Alphabet No. 2 (ITA2). The output ciphertext characters were generated by combining a pseudorandom character-by-character key stream with the input characters using the "exclusive or (XOR)" function (symbolised by ⊕ ).
- Plaintext ⊕ Key = Ciphertext
Similarly, for deciphering, the ciphertext was combined with the same key to give the plaintext.
- Ciphertext ⊕ Key = Plaintext
This produces the essential reciprocity to allow the same machine with the same settings to be used for both enciphering and deciphering.
Each of the five bits of the key for each character was generated by the relevant wheels in two parts of the machine. These were termed the chi () wheels, and the psi () wheels. The chi wheels all moved on one position for each character. The psi wheels also all moved together, but not after each character. Their movement was controlled by the two mu () or "motor" wheels.[12]
The key stream generated by the SZ machines thus had a chi component and a psi component that were combined together with the XOR function. So, the key that was combined with the plaintext for enciphering—or with the ciphertext for deciphering—can be represented as follows.[12]
- Key = Chi-Key ⊕ Psi-Key
Symbolically:
- K = ⊕
The twelve wheels each had a series of cams (or "pins") around them. These cams could be set in a raised or lowered position. In the raised position they generated a "mark" ' x ' (1 in binary), in the lowered position they generated a "space" ' • ' (0 in binary). The number of cams on each wheel equalled the number of impulses needed to cause them to complete a full rotation. It should be noted that these numbers are all co-prime with each other, giving the longest possible time before the pattern repeated. With a total of 501 cams this equals 2501 which is approximately 10151, an astronomically large number.[13] However, if the five impulses are considered independently, the numbers are much more manageable. The product of the rotation period of any pair of chi wheels gives numbers between 41×31=1271 and 26×23=598.
Differencing
Cryptanalysis often involves finding patterns of some sort that provide a way into eliminating a range of key possibilities. At Bletchley Park the XOR combination of the values of two adjacent letters in the key or the ciphertext was called the difference (symbolised by the Greek letter delta 'Δ') because XOR is the same as modulo 2 subtraction (without "borrow")—and, incidentally, modulo 2 addition (without "carry"). So, for the characters in the key(K), the difference ΔK was obtained as follows, where underline indicates the succeeding character:
- ΔK = K ⊕ K
Similarly with the plaintext, the ciphertext and the two components of the key. Also, the relationship amongst them applies when they are differenced. For example, as well as:
- K = ⊕
It is the case that:
- ΔK = Δ ⊕ Δ
If the plaintext is represented by P and the cipertext by Z, the following also hold true:
- ΔZ = ΔP ⊕ Δ ⊕ Δ
And:
- ΔP = ΔZ ⊕ Δ ⊕ Δ
The reason that differencing provided a way into Tunny, was that although the frequency distribution of characters in the ciphertext could not be distinguished from a random stream, the same was not true for a version of the ciphertext from which the chi element of the key had been removed. This is because, where the plaintext contained a repeated character and the psi wheels did not move on, the differenced psi character (Δ) would be the null character (••••• or 00000), or, in Bletchley Park terminology, '/ '. When XOR-ed with any character, this null character has no effect, so in these circumstances, Δ = ΔK. Repeated characters in the plaintext were more frequent both because of the characteristics of German (EE, TT, LL and SS are relatively common),[14] and because telegraphists frequently repeated the figures-shift and letters-shift characters[15] as their loss in an ordinary telegraph message could lead to gibberish.[16]
To quote the General Report on Tunny:
Turingery introduced the principle that the key differenced at one, now called ΔΚ, could yield information unobtainable from ordinary key. This Δ principle was to be the fundamental basis of nearly all statistical methods of wheel-breaking and setting.[1]
Bit-level differencing
As well as applying differencing to the full 5-bit characters of the ITA2 code, it was also applied to the individual impulses (bits). So, for the first impulse, that was enciphered by wheels 1 and 1, differenced at one:
- ΔK1 = K1 ⊕ K1 <>
And for the second impulse:
- ΔK2 = K2 ⊕ K2
And so on.
It is also worth noting that the periodicity of the chi and psi wheels for each impulse (41 and 43 respectively for the first one) is reflected in its pattern of ΔK. However, given that the psi wheels did not advance for every input character, as did the chi wheels, it was not simply a repetition of the pattern every 41 × 43 = 1763 characters for ΔK1, but a more complex sequence.
Turing's method
In July 1942 Turing spent a few weeks in the Research Section.[17] He had become interested in the problem of breaking Tunny from the keys that had been obtained from depths.[3] In July, he developed the method of deriving the cam settings from a length of key.[1] It involved an iterative, almost trial-and-error, process. It relied on the fact that when the differenced psi character is the null character (••••• or 00000), /, then XOR-ing this with any other character does not change it. Thus the delta key character gives the character of the five chi wheels (i.e. Δ = ΔK).
Given that the delta psi character was the null character half of the time on average, an assumption that ΔK = Δ had a 50% chance of being correct. The process started by treating a particular ΔK character as being the Δ for that position. The resulting putative bit pattern of x and • for each chi wheel, was recorded on a sheet of paper that contained as many columns as there were characters in the key, and five rows representing the five impulses of the Δ. Given the knowledge from Tutte's work, of the periodicity of each of the wheels, this allowed the propagation of these values at the appropriate positions in the rest of the key.
A set of five sheets, one for each of the chi wheels, was also prepared. These contained a set of columns corresponding in number to the cams for the appropriate chi wheel, and were referred to as a 'cage'. So the 3 cage had 29 such columns.[18] Successive 'guesses' of Δ values then produced further putative cam state values. These might either agree or disagree with previous assumptions, and a count of agreements and disagreements was made on these sheets. Where disagreements substantially outweighed agreements, the assumption was made that the Δ character was not the null character /, so the relevant assumption was discounted. Progressively, all the cam settings of the chi wheels were deduced, and from them the psi and motor wheel cam settings.
As experience of the method developed, improvements were made that allowed it to be used with much shorter lengths of key than the original 500 or so characters.[1]
See also
References and notes
- 1 2 3 4 Good, Michie & Timms 1945, p. 313 in Testery Methods 1942-1944
- ↑ Government Code and Cypher School 1944, p. 89
- 1 2 Copeland 2006, p. 380
- ↑ Good, Michie & Timms 1945, p. 309 in Early Hand Methods
- ↑ Hodges 1992, pp. 230–231
- ↑ Copeland 2006, pp. 380–382
- ↑ Churchhouse 2002, p. 4
- ↑ Tutte 1998, p. 5
- ↑ Good 1993, p. 161
- ↑ Copeland 2006, p. 381
- ↑ Sale, Tony, The Lorenz Cipher and how Bletchley Park broke it, retrieved 21 October 2010
- 1 2 Good, Michie & Timms 1945, p. 7 in German Tunny
- ↑ Churchhouse 2002, p. 158
- ↑ Singh, Simon, The Black Chamber, retrieved 28 April 2012
- ↑ Newman c. 1944 p. 387
- ↑ Carter, p. 3
- ↑ Tutte 2006, pp. 359, 360
- ↑ Copeland 2006, p. 385 which reproduces a 3 cage from the General Report on Tunny
Bibliography
- Carter, Frank, Bletchley Park Technical Papers: Colossus and the Breaking of the Lorenz Cipher (PDF), retrieved 28 January 2011
- Churchhouse, Robert (2002), Codes and Ciphers: Julius Caesar, the Enigma and the Internet, Cambridge: Cambridge University Press, ISBN 978-0-521-00890-7
- Copeland, Jack (2006), "Turingery", in Copeland, B. Jack, Colossus: The Secrets of Bletchley Park's Codebreaking Computers, Oxford: Oxford University Press, ISBN 978-0-19-284055-4
- Good, Jack (1993), "Enigma and Fish", in Hinsley, F.H.; Stripp, Alan, Codebreakers: The inside story of Bletchley Park, Oxford: Oxford University Press, ISBN 978-0-19-280132-6
- Good, Jack; Michie, Donald; Timms, Geoffrey (1945), General Report on Tunny: With Emphasis on Statistical Methods, UK Public Record Office HW 25/4 and HW 25/5, retrieved 15 September 2010 That version is a facsimile copy, but there is a transcript of much of this document in '.pdf' format at: Sale, Tony (2001), Part of the "General Report on Tunny", the Newmanry History, formatted by Tony Sale (PDF), retrieved 20 September 2010, and a web transcript of Part 1 at: Ellsbury, Graham, General Report on Tunny With Emphasis on Statistical Methods, retrieved 3 November 2010
- Government Code and Cypher School (1944), The Bletchley Park 1944 Cryptographic Dictionary formatted by Tony Sale (PDF), retrieved 7 October 2010
- Hodges, Andrew (1992), Alan Turing: The Enigma, London: Vintage, ISBN 978-0-09-911641-7
- Newman, Max (c. 1944), "Appendix 7: Δ-Method", in Copeland, B. Jack, Colossus: The Secrets of Bletchley Park's Codebreaking Computers, Oxford: Oxford University Press, ISBN 978-0-19-284055-4 Check date values in:
|date=(help) - Tutte, William T. (2006), "My Work at Bletchley Park", in Copeland, B Jack, Colossus: The Secrets of Bletchley Park's Codebreaking Computers, Oxford: Oxford University Press, ISBN 978-0-19-284055-4
- Tutte, W. T. (19 June 1998), Fish and I (PDF), retrieved 7 October 2010 Transcript of a lecture given by Prof. Tutte at the University of Waterloo